Why this matters: 95% of cybersecurity breaches in 2025 involved human error. Mastering these advanced techniques can prevent multi-million dollar losses and protect organizational assets. You are the last line of defense.
🎯 Attention Activity: Can You Spot the Advanced Threat?
Interactive Challenge: Click on suspicious elements in this sophisticated phishing email to reveal hidden threats.
Dear Valued Employee,
Our IT Security team has detected unusual login patterns associated with your account from an unrecognized IP address in Eastern Europe. For your protection, we've temporarily restricted access to your company resources.
To restore full access within the next 2 hours, you must immediately verify your identity by updating your multi-factor authentication settings.
Click here to verify your account now or your account will be permanently deactivated by end of business today.
This is a mandatory security protocol in compliance with our new cyber insurance requirements. Failure to comply may result in account suspension and HR review.
Thank you for your immediate attention to this critical security matter.
IT Security Operations Team
Your Company IT Department
Support Hotline: +1-555-0199 (Available 24/7)
This is a simulated advanced phishing email combining multiple social engineering tactics. Let's deconstruct professional-grade attacks like this.
🌐 The Advanced Threat Landscape (2025)

Modern cyber threats are no longer simple mass emails. Attackers use sophisticated, multi-stage campaigns leveraging AI, deep fake technology, and extensive reconnaissance.
AI-Powered Phishing
Machine learning generates contextually perfect emails with zero grammar errors
CriticalDeep Fake Vishing
AI voice cloning replicates executives for phone-based social engineering
HighAPT Campaigns
Advanced Persistent Threats: long-term infiltration with nation-state resources
CriticalSupply Chain Attacks
Compromising trusted vendors to infiltrate target organizations
High📊 Real-Time Threat Statistics (2025)
of cyberattacks start with a successful phishing email
average cost of a data breach in 2025 (IBM Security)
increase in AI-generated phishing emails since 2023
🎯 Advanced Attack Taxonomy & Techniques
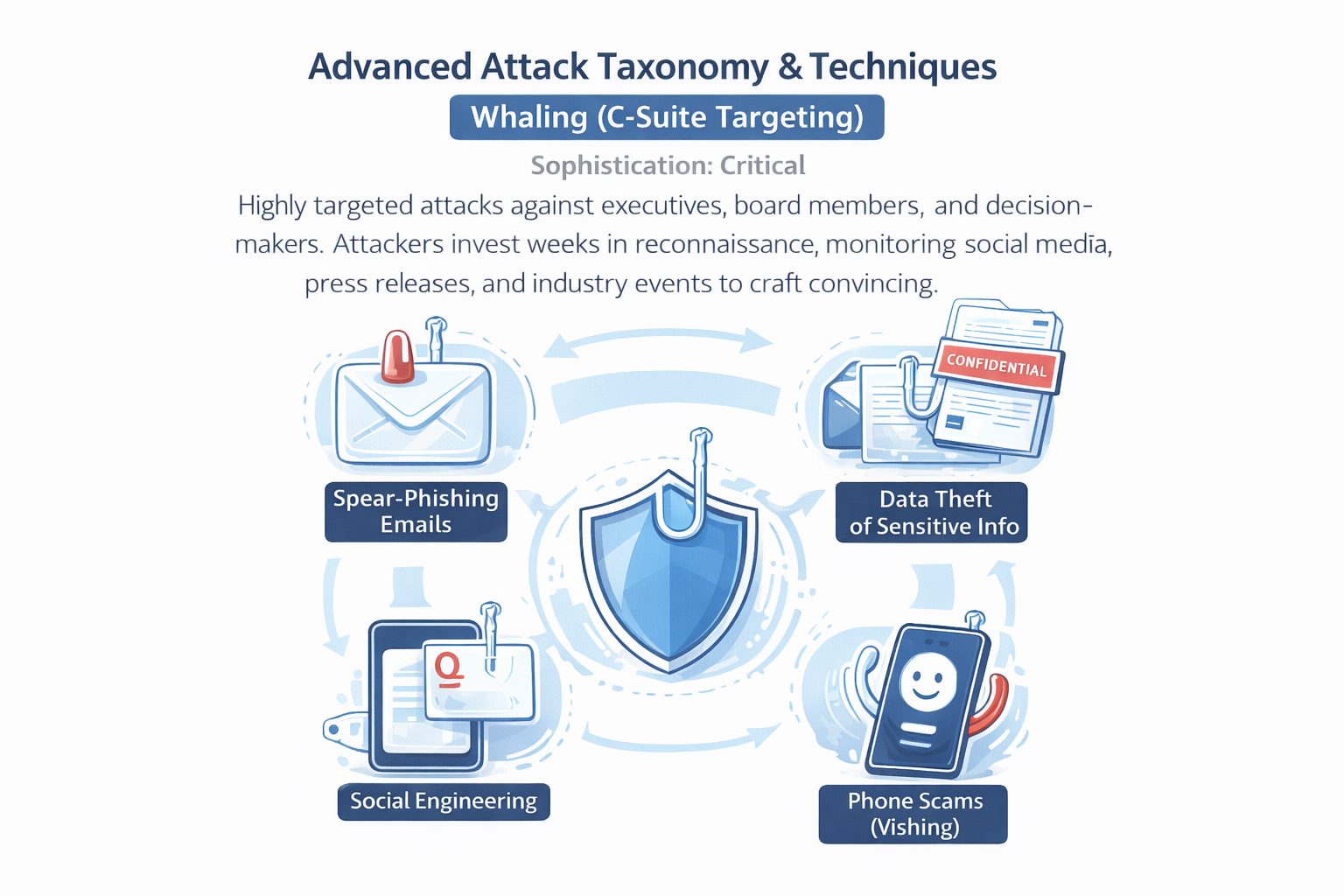
🔴 Whaling (C-Suite Targeting)
Sophistication: Critical
Highly targeted attacks against executives, board members, and decision-makers. Attackers invest weeks in reconnaissance, monitoring social media, press releases, and industry events to craft convincing scenarios.
Example: CEO receives "confidential" M&A documents requiring urgent review, with links to credential-harvesting sites mimicking Box or DocuSign.
🟠 Business Logic Attacks
Sophistication: High
Exploiting organizational processes rather than technical vulnerabilities. Attackers understand your approval workflows, vendor payment systems, and reporting hierarchies.
Example: Fake "vendor" sends invoice with legitimate company format, knowing your AP department processes invoices under $5,000 without manager approval.
🟡 Conversation Hijacking
Sophistication: High
Attackers compromise one account and monitor email threads for weeks, then inject themselves into legitimate conversations at strategic moments.
Example: After monitoring a 3-week contract negotiation thread, attacker sends "updated payment instructions" from the compromised CFO account.
🔵 Watering Hole Attacks
Sophistication: Medium
Compromising websites frequently visited by target employees (industry forums, professional associations, news sites) to deliver malware or harvest credentials.
Example: Attackers compromise a niche industry blog read by your engineering team, injecting credential-stealing JavaScript.
🧠 Advanced Social Engineering Psychology
- Authority Exploitation: Impersonating trusted figures (CEO, IT admin, legal counsel) to bypass critical thinking
- Scarcity Pressure: "Limited time offer" or "account will be closed" to force hasty decisions
- Social Proof: "All employees must complete this by EOD" creates herd mentality
- Reciprocity Manipulation: Offering something valuable (security update, bonus info) to establish "debt"
- Consistency Bias: Referencing past interactions or projects to build false legitimacy
✓ Advanced Knowledge Check
An attacker monitors your company's email for 6 weeks, then injects a fraudulent payment request into an ongoing legitimate thread between your CFO and a vendor. This is an example of:
🔍 Advanced Detection & Analysis Framework
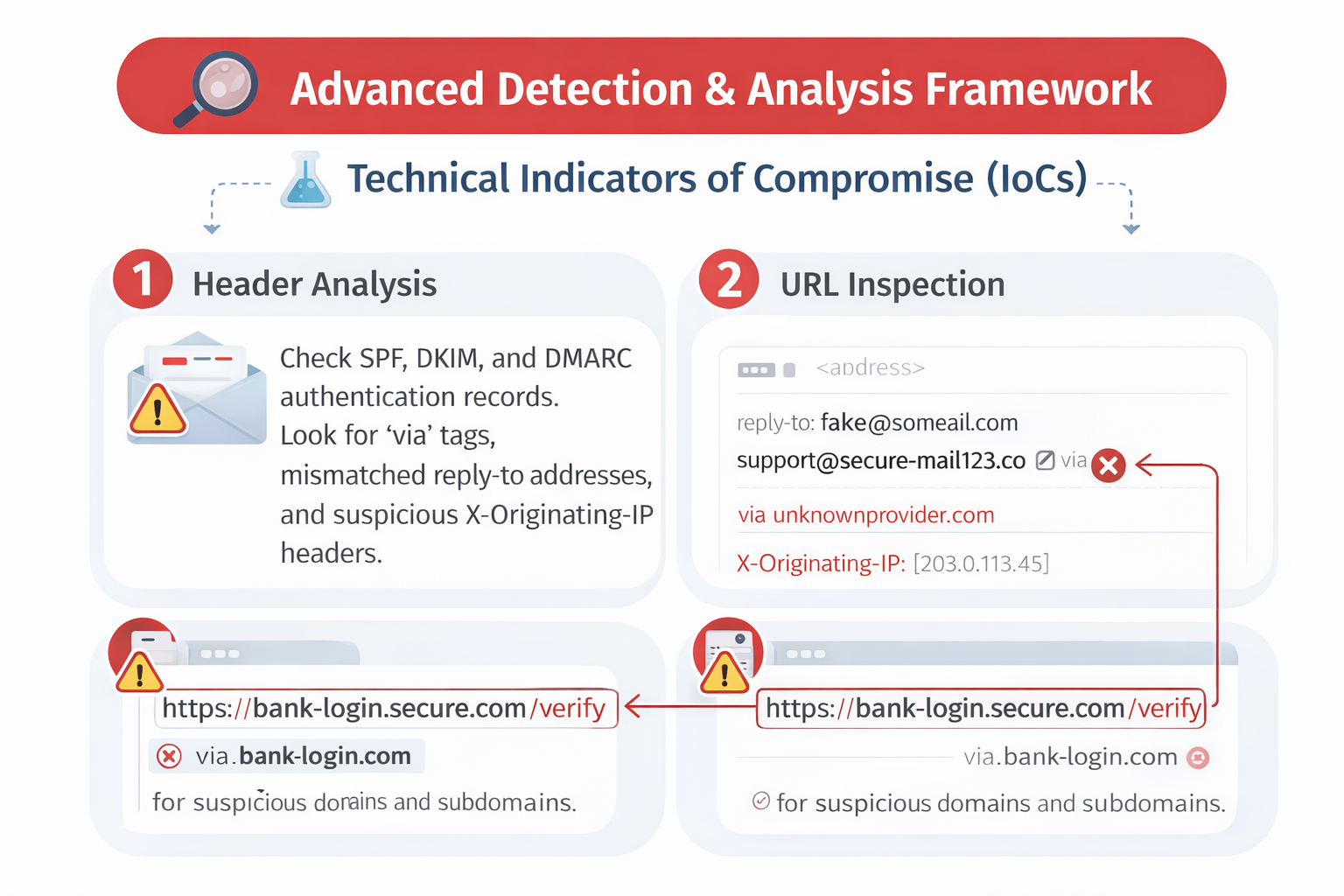
🔬 Technical Indicators of Compromise (IoCs)
- Header Analysis: Check SPF, DKIM, and DMARC authentication records. Look for "via" tags, mismatched reply-to addresses, and suspicious X-Originating-IP headers.
- URL Inspection: Examine full URLs (not just hover preview). Look for homograph attacks (using Cyrillic characters: аmazon.com vs amazon.com), subdomain tricks (amazon.com.phishing.site), and URL shorteners concealing destination.
- Attachment Forensics: Check file extensions (double extensions like "invoice.pdf.exe"), macro-enabled documents from external sources, password-protected archives (bypass scanners), and executable files disguised as documents.
- Language Pattern Analysis: AI-generated content often lacks contextual nuance, uses overly formal language, or contains subtle semantic errors that humans miss but analysis tools detect.
🧩 Behavioral Red Flags
- Process Deviation: Any request that bypasses standard workflows (urgent wire transfers, IT asking for passwords via email)
- Temporal Anomalies: Emails sent at unusual hours (3 AM from your "CEO"), immediate responses to complex requests, or artificially tight deadlines
- Tone Inconsistency: Communication style that doesn't match known patterns (your normally casual manager suddenly formal, or vice versa)
- Multi-Channel Confirmation Absence: Legitimate urgent requests are confirmed via multiple channels; phishing relies on single-channel pressure
🛡️ Advanced Verification Protocol (AVP)
- Pause & Assess (10 seconds): Resist urgency pressure. Take a breath.
- Source Verification: Contact sender via known phone number or in-person—never use contact info from the suspicious message.
- Domain Validation: Manually type official website URL; don't click links. Verify sender domain matches organizational records.
- Request Analysis: Ask: "Does this match established procedures?" If not, escalate immediately.
- IT Consultation: When in doubt, forward to security team BEFORE taking action.
🎮 Advanced Interactive Scenario: APT Campaign
Context: You're a senior financial analyst. You've been exchanging emails with your CFO about Q4 projections. You receive this email:
Hi [Your Name],
Thanks for the updated projections. I reviewed them with the board this morning and they'd like to see the detailed breakdown by product line before our 2 PM call.
I'm tied up in back-to-back meetings, but I need you to upload the detailed Excel files to this secure board portal so they can review: [Link appears to be: yourcompany-boarddocs.sharepoint.com]
Use your normal credentials—IT set this up last week as part of the new board reporting process. Let me know once you've uploaded and I'll notify the board.
Time-sensitive—need this by 1 PM latest.
Thanks,
[CFO's actual name]
CFO, [Your Company]
⚠️ Analysis: What are the red flags here?
This is a sophisticated attack. Click to reveal each red flag:
What should you do?
🚨 Advanced Incident Response Protocol
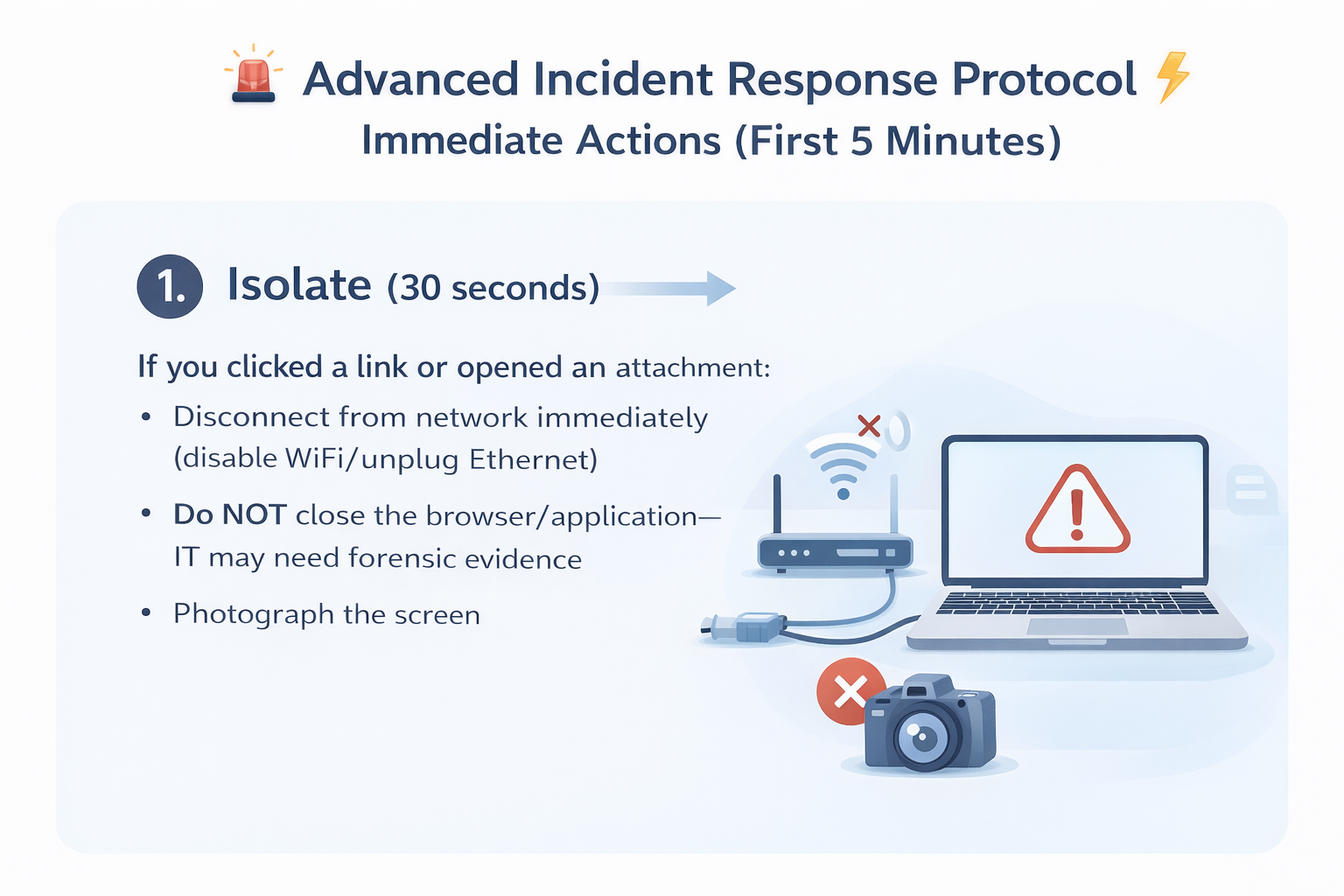
⚡ Immediate Actions (First 5 Minutes)
1. Isolate (30 seconds)
If you clicked a link or opened an attachment:
- Disconnect from network immediately (disable WiFi/unplug Ethernet)
- Do NOT close the browser/application—IT may need forensic evidence
- Photograph the screen with your phone for documentation
2. Alert (1 minute)
Contact your incident response team immediately:
- Call (don't email) IT Security hotline
- Use emergency incident reporting system if available
- Send encrypted message to security team via Signal/WhatsApp
3. Document (3 minutes)
While waiting for IT response:
- Note exact time you received message and when you clicked
- Screenshot the full email (including headers)
- Write down what information you provided (if any)
- List what systems/accounts you've accessed today
🔒 Advanced Containment Measures
- Credential Rotation: Immediately change passwords for all critical systems from a DIFFERENT device
- Session Termination: Force logout all active sessions from compromised accounts
- MFA Reset: Regenerate 2FA codes and backup codes for affected accounts
- Forensic Preservation: Do not delete or modify the suspicious message—IT needs it for threat intelligence
📋 Post-Incident Analysis (Within 24 Hours)
- Root Cause Analysis: How did the attack bypass defenses? What made it convincing?
- Scope Assessment: What data/systems were potentially compromised?
- Control Enhancement: What technical/procedural controls would prevent recurrence?
- Team Learning: Share sanitized case study with organization (without blaming victim)
✓ Advanced Knowledge Check
You receive what appears to be a legitimate email from your bank's security team, with correct branding and a domain that shows "chase.com" when you hover. However, when you check the full headers, you see the email originated from "chase.com.securityalert.net". This is an example of:
🏢 Enterprise Defense Architecture

🛡️ Multi-Layer Defense Strategy
Email Gateway Filtering
Advanced threat protection: URL rewriting, sandboxing, reputation analysis
AI-Powered Detection
Machine learning models analyze communication patterns for anomalies
Continuous Training
Simulated phishing campaigns with real-time feedback and coaching
Zero Trust Architecture
Assume breach: verify every request regardless of source or location
📡 Threat Intelligence Integration
Effective security programs integrate real-time threat intelligence from:
- OSINT Feeds: Open-source intelligence on emerging campaigns and IOCs
- Industry ISACs: Information Sharing and Analysis Centers for sector-specific threats
- Vendor Threat Labs: Research from Microsoft, Google, Proofpoint, Mimecast
- Dark Web Monitoring: Tracking credential dumps and threat actor communications
- MITRE ATT&CK Framework: Standardized taxonomy of adversary tactics and techniques
🔄 Continuous Improvement Cycle
- Metrics Collection: Track click rates, report rates, time-to-report for simulated campaigns
- Vulnerability Identification: Which departments/roles are highest risk?
- Targeted Training: Personalized content based on individual risk profiles
- Control Testing: Red team exercises and tabletop simulations
- Process Refinement: Update procedures based on lessons learned
📚 Case Study: The $100M BEC Breach
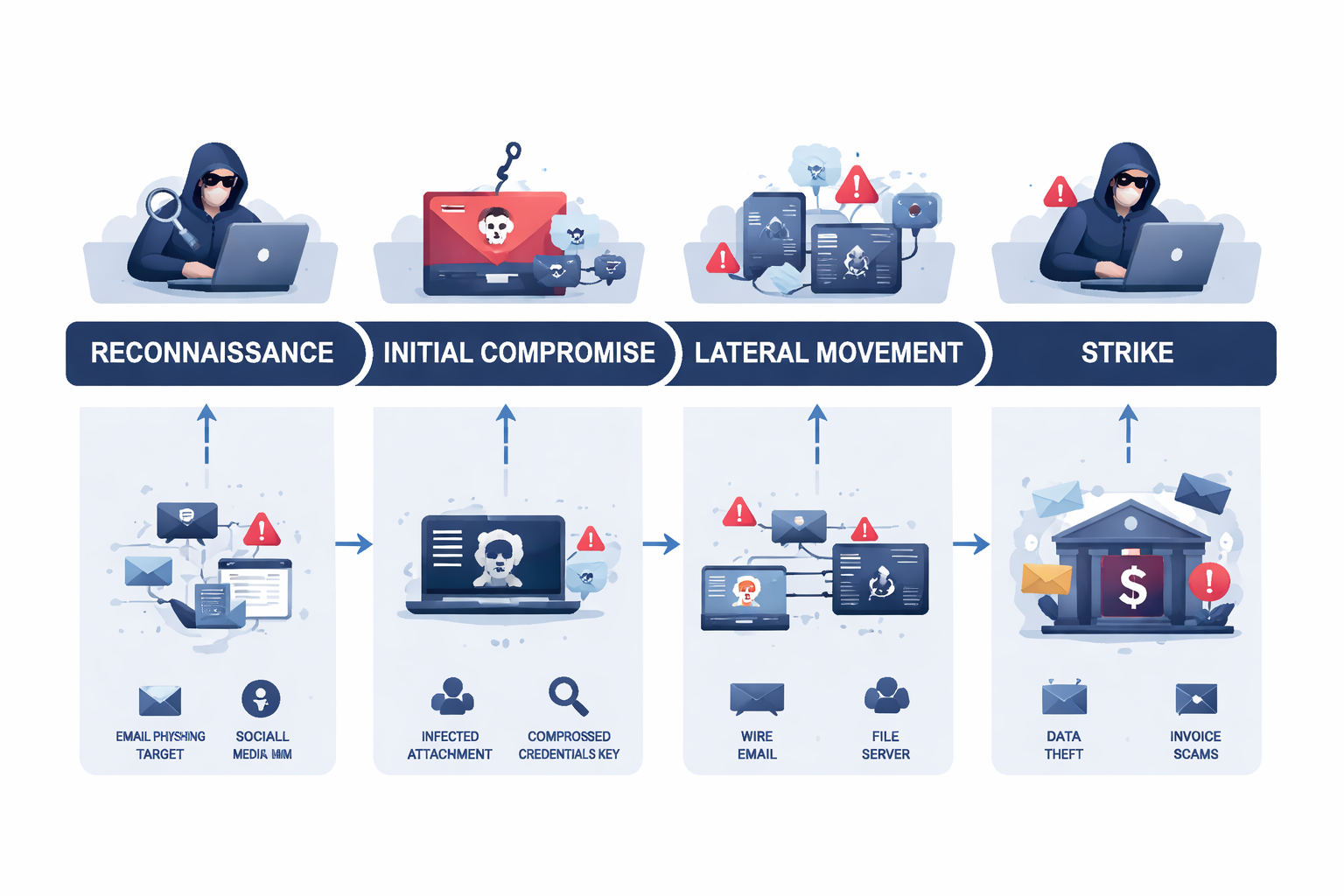
Background: In 2024, a Fortune 500 technology company lost $100 million in a sophisticated BEC attack that bypassed all technical controls.
🎯 The Attack Timeline
Week 1-4: Reconnaissance
Attackers created fake LinkedIn profiles posing as recruiters and connected with 50+ company employees, gathering intel on organizational structure, ongoing projects, and executive communication styles.
Week 5-8: Initial Compromise
Spear phishing campaign targeting IT help desk staff with fake Microsoft 365 security alerts. One staff member's credentials compromised via credential harvesting site.
Week 9-16: Lateral Movement
Using compromised IT credentials, attackers gained access to email systems and monitored executive communications for 7 weeks, learning about a pending acquisition deal.
Week 17: The Strike
During acquisition negotiations, attackers sent email from compromised CFO account to accounting team: "CEO approved urgent wire transfer for acquisition deposit—use new escrow account below." Instructions looked identical to previous legitimate transfers.
Week 17-18: Discovery
$100M transferred to attacker-controlled account. Real CFO discovered the fraud 36 hours later when actual escrow company inquired about delayed payment. Funds had already been distributed across 27 international accounts.
🔍 What Failed?
- No Out-of-Band Verification: Finance team accepted email instruction without phone confirmation (process existed but wasn't enforced for "urgent" requests)
- Insufficient Privilege Segmentation: IT help desk had excessive access to executive email systems
- Delayed Anomaly Detection: $100M transfer was flagged but approved because it matched "acquisition context"
- Inadequate User Training: IT staff not trained to recognize advanced credential harvesting techniques
✅ What Could Have Prevented This?
- Mandatory Dual Authorization: All wire transfers > $50K require two independent approvals via different channels (email + voice confirmation)
- Zero Trust Network Access: Limit IT help desk access to only essential systems, require MFA for privileged escalation
- Behavioral Analytics: AI monitoring flagging unusual communication patterns (CFO account sending payment instructions at 2 AM)
- Regular Tabletop Exercises: Simulate BEC scenarios quarterly to test response procedures
Total BEC losses reported to FBI IC3 in 2024
✓ Advanced Knowledge Check
In the $100M BEC case study, what was the MOST critical control failure that allowed the attack to succeed?
🔐 Zero Trust Security Model
Core Principle: "Never trust, always verify"—regardless of whether the request comes from inside or outside the network.
🏗️ Zero Trust Architecture Pillars
Identity Verification
Multi-Factor Authentication (MFA): Something you know (password) + something you have (phone/token) + something you are (biometric)
Device Trust
Endpoint Security: Only managed, compliant devices with current patches and security software can access resources
Network Segmentation
Micro-Segmentation: Limit lateral movement by restricting access between network segments
Continuous Monitoring
Behavioral Analytics: Real-time analysis of user and entity behavior to detect anomalies
🛡️ Defense in Depth Strategy
Layered security controls ensure that if one fails, others still protect:
- Perimeter Defense: Firewalls, email gateways, web filters
- Network Defense: Intrusion detection/prevention systems (IDS/IPS)
- Endpoint Defense: Antivirus, EDR (Endpoint Detection & Response), application whitelisting
- Application Defense: Web application firewalls (WAF), input validation, secure coding practices
- Data Defense: Encryption at rest and in transit, DLP (Data Loss Prevention)
- Human Defense: Security awareness training, phishing simulation, incident reporting culture
🎯 Practical Zero Trust for Employees
- Verify Every Request: Even if it comes from a known colleague, verify high-risk actions independently
- Use MFA Everywhere: Enable 2FA on all accounts—work and personal (attackers pivot from personal to work accounts)
- Assume Email is Compromised: Never send passwords, credit cards, or sensitive data via email—use encrypted channels
- Challenge "Normal": If something feels off, trust your instincts and escalate
🤖 AI-Powered Threats & Future Landscape

⚡ AI is Revolutionizing Social Engineering
Increase in AI-generated phishing emails since ChatGPT's release (2023-2025)
🎭 Advanced AI Attack Techniques
🗣️ Voice Deep Fakes
Current State: AI can clone a voice with just 3 seconds of audio. Attackers call employees pretending to be executives, using deep-fake voice technology.
Example: UK company lost $243,000 in 2024 when attackers used deep-fake audio of CEO's voice to authorize fraudulent transfer.
Defense: Establish verbal "code words" with executives for high-risk requests, never rely solely on voice recognition.
📹 Video Deep Fakes
Current State: Real-time video manipulation allows attackers to impersonate executives on video calls.
Example: Hong Kong company lost $25 million in 2024 when attackers used deep-fake video of CFO on Zoom to authorize transfers.
Defense: Use pre-established authentication questions, verify via multiple channels, never act on video-only authorization.
📝 AI-Written Phishing
Current State: Large Language Models (LLMs) generate grammatically perfect, contextually appropriate phishing emails at scale.
Capability: AI analyzes target's writing style from social media/public sources and mimics it perfectly.
Defense: Traditional "grammar check" detection is obsolete. Focus on procedural verification instead.
🔬 Automated Reconnaissance
Current State: AI tools scrape LinkedIn, company websites, social media to build detailed organizational charts and relationship maps.
Capability: In 30 minutes, AI can identify key targets, their projects, colleagues, and optimal social engineering approach.
Defense: Limit publicly shared information, use privacy settings, educate employees on OSINT exposure.
🔮 Emerging Threats (2025-2027)
- Quantum Computing: Future quantum computers could break current encryption standards—organizations preparing "quantum-resistant" cryptography
- IoT Exploitation: Smart office devices (thermostats, cameras, printers) become attack vectors for network infiltration
- AI-Powered Malware: Polymorphic malware that uses AI to adapt and evade detection in real-time
- Synthetic Identity Fraud: AI creates completely fake identities with generated faces, voices, and social media histories
🛡️ AI-Powered Defense
The good news: AI also enhances defense capabilities:
- Anomaly Detection: Machine learning identifies subtle deviations in communication patterns that humans miss
- Predictive Threat Intelligence: AI analyzes global threat data to predict and block emerging campaigns
- Automated Response: Security orchestration, automation, and response (SOAR) platforms respond to threats in milliseconds
- Adaptive Training: AI personalizes security training based on individual vulnerabilities and learning styles
🎯 Key Takeaways: Advanced Cybersecurity Mastery
🔑 Critical Concepts
- 95% of breaches involve human error—you are both the target and the last line of defense
- AI-powered attacks bypass traditional detection—perfect grammar and context no longer indicate legitimacy
- Zero Trust mindset: Verify every high-risk request through independent channels, regardless of apparent source
- APTs and BEC attacks use multi-week reconnaissance—sophistication levels are enterprise-grade
- Out-of-band verification is non-negotiable for financial transactions, credential changes, and sensitive data requests
🛡️ Defensive Frameworks
- Advanced Verification Protocol (AVP): Pause → Verify Source → Validate Domain → Analyze Request → Consult IT
- Immediate response: Isolate → Alert → Document (first 5 minutes after clicking suspicious content)
- Defense in Depth: Layer technical controls with procedural discipline and human vigilance
- Threat Intelligence: Integrate real-time IOCs, industry intelligence, and MITRE ATT&CK framework
💡 Practical Actions
- Enable MFA on all accounts (work and personal)
- Verify financial requests via phone using independently sourced numbers
- Report suspicious emails immediately—no blame, only learning
- Inspect email headers and full URLs before clicking
- Establish verbal authentication codes with executives for urgent requests
- Treat email as inherently insecure—use encrypted channels for sensitive data
📋 Final Assessment: Advanced Cybersecurity Mastery
You are about to begin the advanced certification assessment. This assessment evaluates your mastery of:
- Advanced threat detection and analysis techniques
- Sophisticated social engineering psychology
- Incident response protocols and procedures
- Zero Trust security principles
- AI-powered threat landscape understanding
- Real-world case study analysis
Ready? Click Next to begin the assessment.
📝 Assessment Question 1 of 6
You receive an email appearing to be from your company's IT security team, stating that your Microsoft 365 account has been flagged for suspicious activity and you must click a link to verify your identity within 2 hours. The email domain is "microsoft-security-verification.com". The writing is perfect, and it includes your recent login times. What is the MOST likely attack vector?
📝 Assessment Question 2 of 6
Your CFO's email account has been compromised, and attackers have monitored email for 4 weeks before injecting a fraudulent wire transfer request into an existing legitimate email thread with your accounting team. This technique is called:
📝 Assessment Question 3 of 6
You receive a phone call from someone claiming to be your CEO, requesting urgent approval for a $50,000 payment to a new vendor. The voice sounds exactly like your CEO. According to Zero Trust principles and the lesson content, what should you do FIRST?
📝 Assessment Question 4 of 6
In the $100M BEC case study presented in the lesson, what was the MOST critical control failure that enabled the attack to succeed?
📝 Assessment Question 5 of 6
You accidentally clicked a link in a sophisticated phishing email. According to the Advanced Incident Response Protocol, what should be your FIRST action within the first 30 seconds?
📝 Assessment Question 6 of 6
According to the lesson, what percentage increase in AI-generated phishing emails has occurred since ChatGPT's release (2023-2025)?
🎓 Assessment Complete
Your Score: 0%